WebHost Manager (WHM) offers a useful feature for enhancing email security on Fast VPS server and Dedicated Server Hosting. Administrators can apply filters to incoming emails based on specific countries, regions, and domains, preventing potentially malicious messages from reaching spam filters in cPanel or the end user’s email client. This feature serves as an effective defense in depth strategy to block harmful emails and safeguard your system.
Our Managed VPS Hosting provides top-tier performance, lightning-fast servers, heightened security measures, and maximum up-time to ensure your website or application runs smoothly. Our expert team manages and monitors your virtual private server (VPS) to guarantee optimal performance, with regular backups and security updates to ensure your data is protected. With our Managed VPS Hosting, you can focus on your business while we handle the technical aspects of hosting.
Filter Incoming Emails
Filter Incoming Emails by Nation
Comply with these steps to dam nations or areas from emailing your server.
This may also affect users emailing from a digital private network (VPN).
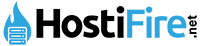
To begin, log in to WHM using root access. Once logged in, navigate to the “Filter Incoming Emails by Country” option located on the left-hand side. To enable or block a single nation, simply toggle the switch to the right. Any changes made are automatically saved.
If you want to block or enable multiple nations simultaneously, choose the “Select All” checkbox at the top or select the checkboxes beside each country you want to modify. Then, select “Block Selected” or “Allow Selected.”
Finally, select “Allowed” or “Blocked” at the top of the page to review any changes made. With these simple steps, you can easily manage incoming emails and improve your email security.
Filter Incoming Emails by Area
Follow these steps to dam domains from emailing your server.
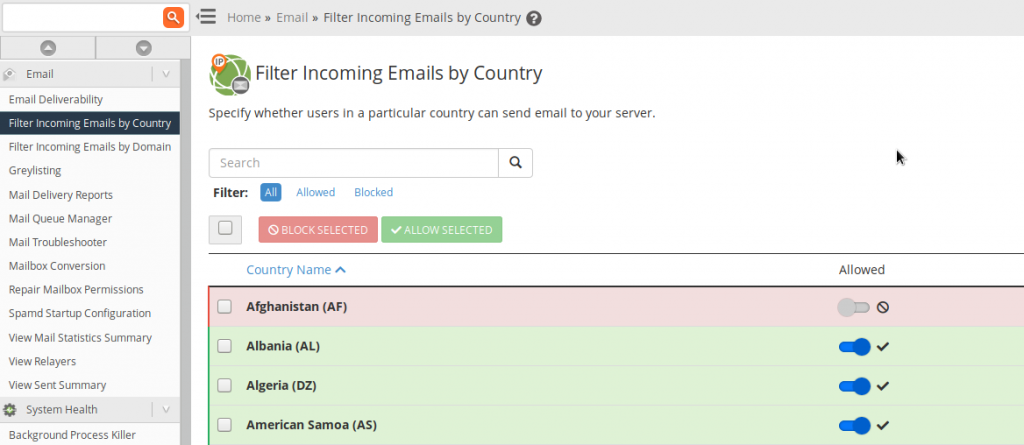
To begin, access WHM as root. Once inside, navigate to the “Filter Incoming Emails by Domain” option located on the left-hand side. From there, you can input the domains you wish to block by typing them into the “Blocked Domains” field (one per line).
If you need to block subdomains for a domain, use an asterisk (*) before the domain name (e.g., *.phishingsite.com). Additionally, if you need to add international domain names (IDNs), make sure to choose the “Present domains as ASCII” option.
Once you’ve made any necessary changes, make sure to save your modifications to the filter. With these straightforward steps, you can easily block incoming emails from specific domains, improving your email security.
Improve E-mail Protection
Once you’ve configured the settings to filter incoming emails, it’s important to take additional steps to enhance your email security. Here are some helpful guides to follow:
Real-time Blackhole Lists (RBLs) are third-party databases that identify suspicious IPs and domains. These lists are regularly updated, and you can add an RBL link to your filter to ensure your list is always up to date.
SpamExperts is a third-party service that can be installed to filter emails through MX record configuration. This helps prevent malicious emails from reaching your server.
Spam Filters (formerly SpamAssassin) can be configured in cPanel to check all incoming emails against preset and customized rules. You can also manage a spam/junk folder and customize filtering to suit your server environment.
Email Filters and Global Email Filters in cPanel can help you manage emails more efficiently by identifying suspicious emails and automatically forwarding them to designated folders for better organization. This feature allows you to set filters for an entire cPanel account or specific email accounts.
Webmail and desktop email clients have built-in filtering options, such as Thunderbird junk settings. Additionally, email software may have plugins available for added spam protection, such as the ClamAV integration for Claws Mail.
You can enhance email authentication by using SPF, DMARC, and other DNS records to mitigate phishing and spoofing emails without manual intervention.
Verizon’s Data Breach Investigations Report (DBIR) provides valuable insights on recent cybersecurity trends and best practices. Review the DBIR to better understand the most targeted cyber attack vectors in your region and how to protect your data at rest and in use.
If you receive a convincing spear-phishing email, it’s important to be aware of the techniques used to manipulate you into sending Bitcoin currency to an unknown entity. You can learn more about this topic in our article on the “this day I hacked your OS” phishing email.
Remember, there are other steps you can take to harden your Linux server beyond spam filtering. For more information on how to secure your managed VPS or cloud server, be sure to explore additional resources available.